Did you know that ADISA is the world’s best ITAD security system certification scheme?
With rapidly evolving and changing IT technologies there are constantly new challenges for IT data security. It is safe to say that the ADISA standard remains at the forefront of data security.
CiRecycling, the ITAD (IT Asset Disposition) arm of Centerprise International, are proud to be certified by ADISA . With Ci you can be sure that we understand all aspects of data protection and all ITAD compliance solutions.
Using an IT Asset Recovery Provider, such as Centerprise International, certified by ADISA for this service is the only way to ensure true GDPR compliance when disposing of your old end-of-life IT hardware. As experts in ITAD, CiRecycling can guide you confidently through the information security and data destruction process.
A new concept called Data Impact Assessment Level (DIAL) was introduced into ADISA Standard 8.0 which came into effect on 1st July 2022.
The new standard 8.0 from ADISA has been approved by the UK’s Independent Commissioners Office and this has been developed to help businesses ensure they have adequate processes in place to protect their data and fulfil all their legal obligations.
Did you know that to be GDPR compliant for the disposal of your old end-of-life IT hardware you should have a written contract signed by both parties which covers:
- The subject matter and duration of the processing
- The nature and purpose of the processing
- The type of personal data and categories of data subjects
- The controller’s obligations and rights
The contract shall include specific terms or clauses regarding
- Processing only on the controller’s documented instructions
- Duty of Confidence
- Appropriate security measures
- Use of sub-processors
- Data subjects’ rights
- Assisting the controller
- End of contract provisions
- Audits and inspections
The contract should include details of the service being provided and include:
- Confirmation of agreed auditing detail
- Agreed sanitisation process by media type
- Agreement for logistical services
- Confirmation that the service issuer is the owner of the hardware and is legally entitled to release the equipment
- Confirmation of the point within the process where the applicant accepts custody of the data
- Designation of the IT Asset Disposal provider as the data processor
- Agreement for any sub-processors.
Data Impact Assessment Level (DIAL)
How can end-users ensure that the service they are getting is in line with the requirements of their business?. Data Impact Assessment Level (DIAL) was introduced into ADISA Standard 8.0 which came into effect on 1st July 2022 and helps to clarify what Data Impact Assessment Level (DIAL) you need for your business. Centerprise International Recycling is here to help you through the process.
Risk can never be removed entirely from a business process and asset recovery is no different. As it is a very physical process, the countermeasures which are put in place can vary and typically result in higher costs for lower risks to the data controller. To ensure the data controller can control their own risk without being determined by cost alone.
The DIAL is assessed by the data controller’s own view on the following:
- Threat
- Risk Appetite
- Category of Data
- Volume of Data
- Impact on them in the event of a data breach.
Each of these variables must be determined by the data controller which will provide them with an overall DIAL rating. This in turn will determine what level of service must be provided by the IT Asset Recovery provider to meet the DIAL rating.
As the DIAL rating must be a controller decision the IT Asset Recovery Provider must have the DIAL rating verified. To allow this Centerprise has a link to the ADISA portal on our website Adisa Certification- DIAL – CiRecycling which controllers can use to create their DIAL rating. This produces a certificate with a unique reference and scope of the DIAL as a rating can be present for all data controller assets, a specific location or just a one-off collection.
Four main variables are assessed to then overlay against the overall impact of a data breach which will then create the DIAL rating for the data controller which can then be used to identify a suitable supplier and specification of service.
Threat
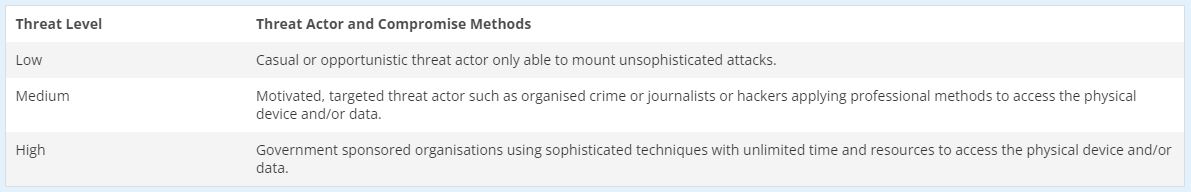
The first variable is threat and will be based on a threat matrix already being used. A data controller must determine who they feel their most likely threat adversary is. This can be aligned to the overall Cyber Threat Analysis but must consider the business process itself and whether the data controller feels asset recovery is a specific threat vector which has actors seeking to exploit. Threat will generally be determined by the industry the data controller operates in and the data which it holds which will help identify actors who may seek to gain access to the data for reasons of financial gain, intellectual property theft or any other purpose.
Risk Appetite
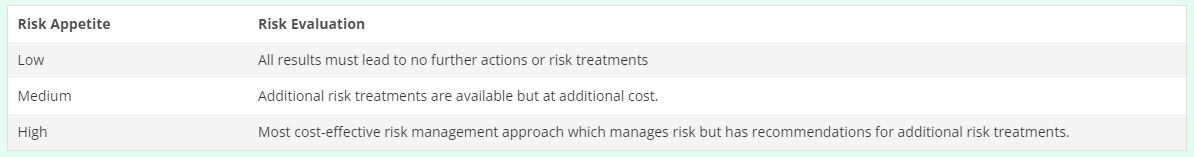
Second variable is risk appetite which is a metric determined by the level of risk which a company is allowed to pervade into business operations in order to achieve its business objectives. Risk management refers to risk appetite as the “Amount and type of risk that an organisation is prepared to pursue, retain or take”.
Categories of Data
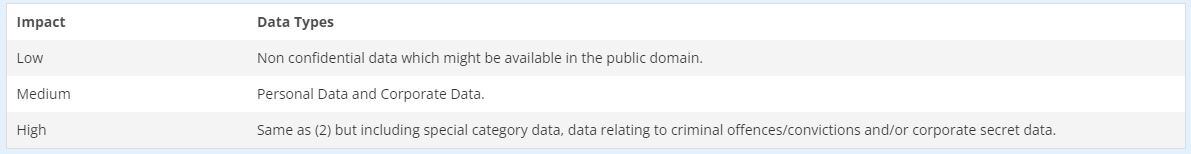
The third variable concerns the categories of data being processed which are aligned to the categories within the UK GDPR.
Volume of Data
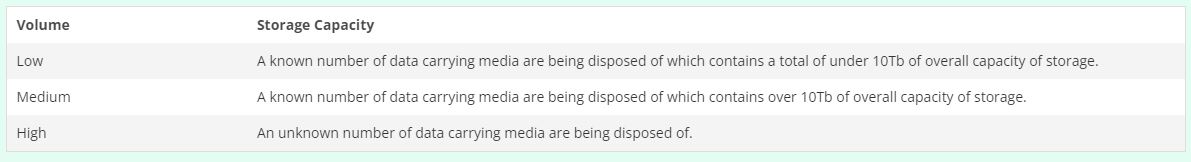
The final main variable is the volume of data being processed within the business process. This will enable the data controller to determine the aggregated risk within the business process.
As this business process is focussed on storage media it is the overall storage capacity which is the critical factor. The data controller will need to determine how much storage capacity is being presented to the IT Asset Recovery Provider.
Business Impact
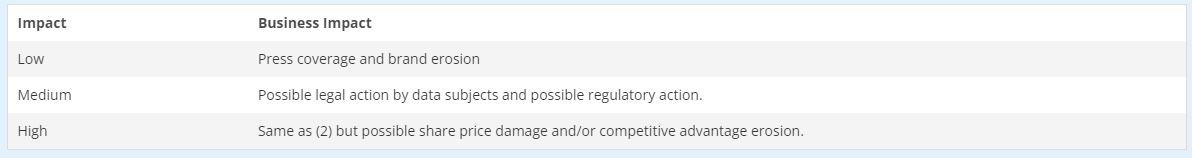
The data controller should then look at the business impact which a data breach would have on their business. This will be dependant on the type of business, the scale of operations, the profit the business has, and of course, the type of data being processed.
Data Impact Assurance Level
If a data controller has a DIAL rating of 2 they should only use an IT Asset Recovery Provider which has been certified to a DIAL 2 or 3 service capability. Centerprise International have DIAL 2 and 3 capacity and is ready to help you through the process, to ensure compliance with all data regulations. Our full accreditations are listed here.
Extending the Life of Your IT Equipment
Decommissioning IT equipment does not mean that it is the end of the lifecycle of that hardware. We find that many of our customers are working smarter by extending the life of their IT equipment. We can ensure that best practice for data destruction is followed when redeploying IT within your organisation (or for resale) to preserve data security and fulfil all your data obligations. We can eliminate the risk of data loss thanks to our full chain of custody and asset tracking. Our IT lifecycle management services provide a comprehensive solution for the decommissioning, tracking and disposal of IT assets.

